As a leading provider of software services and semiconductors to the global access control markets, LEGIC has developed mature, high-security software and semiconductors that ensure only authorized persons have access to offices, schools, airports, and hotel rooms to name only a few examples.
Imagine the millions of electronic doors installed around the world that securely authenticate hundreds of millions of authorized users (via “electronic credentials”) every day based on LEGIC technology!
Taking this concept one step further, the secure authentication of users via their electronic credentials extends far beyond the opening of doors: virtually any piece of infrastructure that must be restricted to specific users can take advantage of LEGIC’s credentialing technology.
Some examples include:
- Mobility vehicles: leveraging electronic credentials for shared vehicles (car sharing, rental vehicles, e-scooters, etc.) to ensure only authorized, paying customers have access, and at the right time.
- Industrial machines: production equipment, forklifts, robots, containers etc. which must only be operated by authorized personnel.
- Shared IT equipment: granting employees and visitors access to shared printers, computer terminals etc.
Traditionally, authorization to use all these things has been done via smartcards using RFID, better known as employee badge, hotel card key, etc. In recent times, however, the smartphone is replacing the smartcard due to several reasons:
- Everyone has a smartphone, so an additional card that can be easily forgotten or lost is not necessary (not many people forget to take their smartphone with them!).
- Smartphones support biometric identification such as facial recognition which adds a layer of security not natively supported by smartcards.
- Smartphones can host complementary applications that add value to the to service provider’s offering – for example a smartphone hotel room key app can also push customer loyalty offerings directly to a guest’s smartphone display such as restaurant discounts and other special offers.
- Longer distance – thanks to Bluetooth® Low Energy, smartphones can be authenticated over distances up to 10 meters, vs. just a few centimeters for smartcards.
LEGIC Connect: secure contactless authentication via smartphone
LEGIC Connect, our most popular mobile service, is a software trusted service that provides instant, secure distribution of credentials or other sensitive data to authorized smartphones – anytime, anywhere and instantly at the touch of a button. It is a security enabler for any mobile service and fulfills current and future needs for security. By integrating LEGIC Connect into existing infrastructures, a smartphone can become anything – a door opener, train ticket, time & attendance tracker, city pass, car or hotel key, and much more.
End-to-end security between users and the infrastructure 24/7
Mobile services which interact with users via their smartphones leverage LEGIC Connect to:
- Protect infrastructure and personal credentials
This is the most important issue when it comes to mobile services and is crucial when connecting users via smart devices to sensitive and costly assets.
- Enable fully automated business models which require 24/7 real-time processing of credentials. Such services require dynamic changes on-the-fly as well as seamless integration of an unlimited number of users, for example an automated parking garage that is open around the clock.
Why is LEGIC Connect so popular?
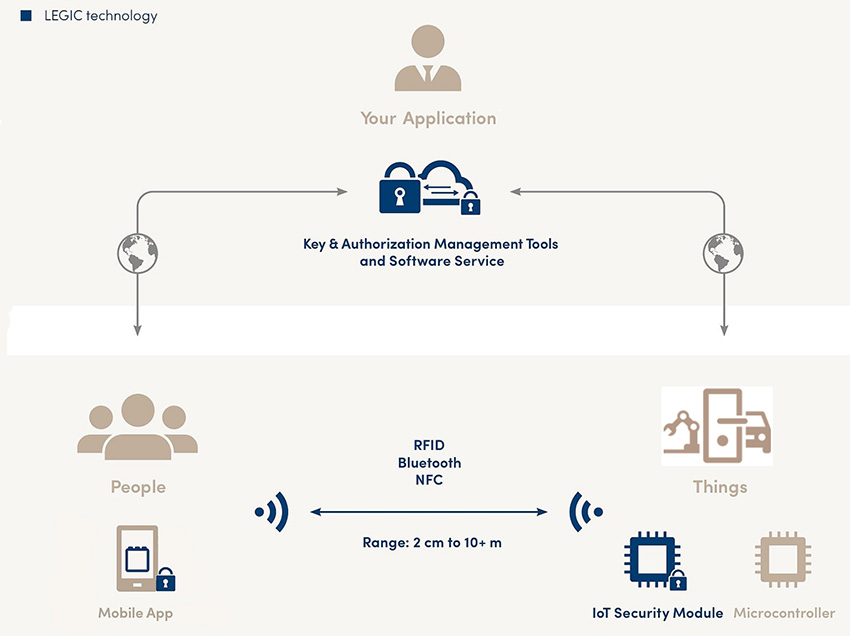
LEGIC Connect combines off-the-shelf hardware and software components which can be simply integrated into mobile business models requiring user authentication. It easily integrates users and infrastructure according to service provider requirements.
The software service communicates directly with LEGIC security modules implementing secure element technology embedded in infrastructure such as doors, vehicles, printers, lockers, POS terminals, etc . The platform fulfills the highest security standards for end-to-end encryption (i.e AES) and thus protects against the increasing threat of hacker attacks. Customer specific data packages can be transferred securely, so that interaction is not limited to a predefined set of commands.
LEGIC Connect also allows service providers to combine RFID or NFC-HCE and Bluetooth technology in the same eco-system or upgrade their existing business model with one or the other.
Popular applications for LEGIC Connect:
Corporate access
LEGIC Connect alone or as an addition to existing smartcard infrastructure adds a highly dynamic assignment and withdrawal of access rights, saving time and costs. Temporary access can be given to visitors, customers or contractors within seconds. With LEGIC Connect, these scenarios can be easily realized.
Hospitality
In the hotel industry, customer experience is at the forefront. For hotels, mobile room keys are fundamental for several major benefits: Guests don’t need to check-in at the reception and wait for their key cards. Booking their favorite room in advance and receiving the keys directly on their smartphones or changing a room without waiting in line at the reception are just a few of the many benefits.
Mobility
Mobility business models like vehicle sharing, e-charging or fleet management serve new concepts for individual or corporate mobility. All of these services can quickly integrate any user via a simple app download. LEGIC Connect allows the secure creation and instant deployment of virtual car keys, fleet access rights, e-charging credentials or the like on smartphones.
Almost any infrastructure application
Corporate access, hospitality, mobility, residential access, industrial IoT etc. are just a few possible use cases. Thanks to LEGIC’s innovative and multi-technology platform, every user can be connected via his or her smartphones to any “thing”.

For more details about LEGIC Connect, visit https://www.legic.com/security-platform/mobile-credentialing or email info@legic.com.